Architecture audit
A technical architecture audit to reinforce the security of your IT infrastructure.
Identify vulnerabilities for a compliant architecture
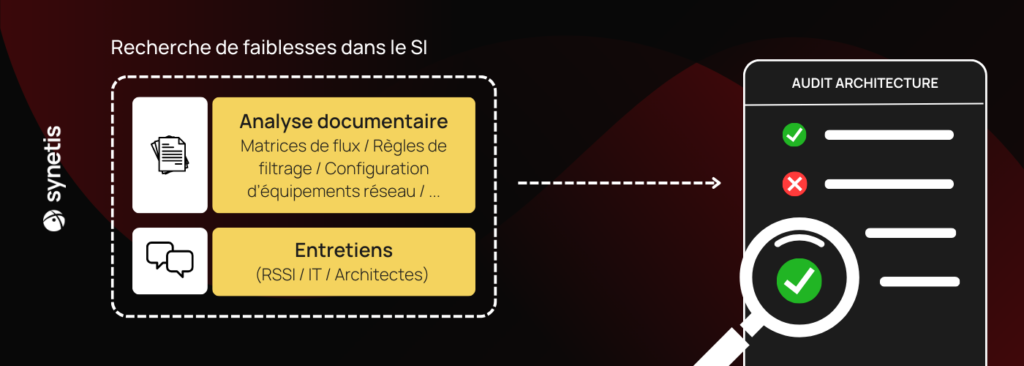
The aim of an architecture audit is to identify weaknesses or non-compliance with recommended security practices.
An architecture audit is based on a documentary analysis followed by interviews with the people in charge of the design, implementation, administration, supervision and maintenance of the target information system.
In addition, additional analyses can be carried out on network configuration samples (e.g. switches, firewalls, security cloud groups, etc.) to complete the audit.
Discover the benefits of a technical architecture audit
- Identification of potential risks within the audited perimeter;
- An action plan including recommended remedies in the specific context of the target system;
- Enhanced protection for your data.
- Optimizing IT resources.
- Verify the security of your architecture to prevent future incidents.
As Synetis is a PASSI-qualified company, the architecture audit can be carried out under this qualification as defined by ANSSI. This applies, for example, to the audit of a Restricted Diffusion network or a SecNumCloud qualification.
Rely on a rigorous, proven approach
During an architecture audit, the following aspects in particular are checked (non-exhaustive list):
Our methodology is based on the various technical guides and recommendations issued by ANSSI (Agence Nationale de la Sécurité des Systèmes d’Information). At every point of the infrastructure, our auditors’ attention is focused on the coverage of Information Systems Security (ISS) requirements, i.e. : Availability, Integrity, Confidentiality and Traceability.
Any operational constraints and business needs in the application of these guides and their associated recommendations are taken into account by our auditors.
Literature review
This part of the audit consists of comparing your documentation with the selected standards. Our audit team uses the various mappings provided to analyze your security.
- Mapping information system administration ;
- Logical network mapping ;
- Application mapping ;
- Physical mapping of the network.
Interviews with teams
Carrying out an audit also requires discussions around the business context of the audited perimeter and questions to clarify the auditors’ and teams’ understanding of the documentation received.
Additional questions can also be asked on less technical aspects.
Find out more about real-world security solutions based on our expertise in the field.
- Unsatisfactory partitioning (risk of lateral displacement) ;
- Lack of separation between critical services ;
- Little or no filtering of incoming and/or outgoing flows;
- No nomadic access control ;
- No system hardening ;
- No maintenance policy procedures ;
- No centralization and/or supervision of logs ;
- Exposure of internal cloud services to the Internet.
Carrying out an architecture audit is an essential investment for any company wishing to verify and improve the security of its infrastructure. By identifying and correcting vulnerabilities, you can significantly reduce the risk of incidents while improving the performance of your IT department.