Build your sensitive or sovereign information systems
Guarantee your strategic independence from extraterritorial legislation
Control every step in securing
your sensitive or sovereign information system
Frame and design your sensitive IS (related to IGI1300, II901, etc.)
Deploy and maintain your sensitive IS over time
Audit and approve your sensitive IS, at DR or LPM level
Regain independence and sovereignty by deploying French or European security bricks
Build a robust, self-sufficient digital sanctuary
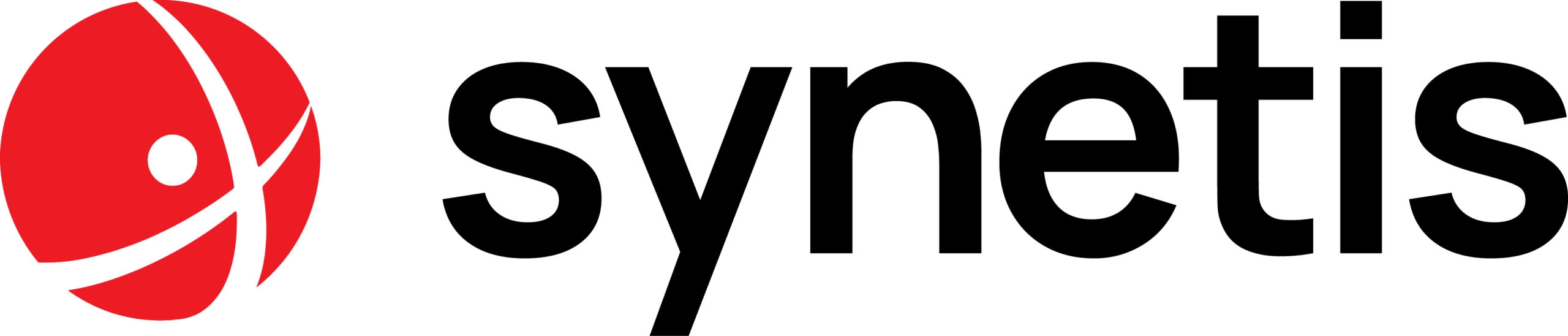
Sensitive information systems
Both a legal obligation and a pillar of your defense posture, compliance with IGI 1300 and II 901 is the essential foundation for protecting your most sensitive data. Implementing these measures can quickly become a complex challenge for your organizations.
- Simplify your compliance process: we offer you customized support to translate your constraints into concrete action plans;
- Security and certification : we secure your path to certification while guaranteeing total watertightness for your most sovereign environments.
Securing excellence: compliance without compromise
Mastering regulatory issues
Let us help you translate the many complex regulatory requirements into concrete measures
Trust architecture
Rely on a firm of experts in cybersecurity and secrecy protection to build a watertight, compliant information system.
360° support
Manage the project from start to finish, from scoping to deployment and certification of the information system
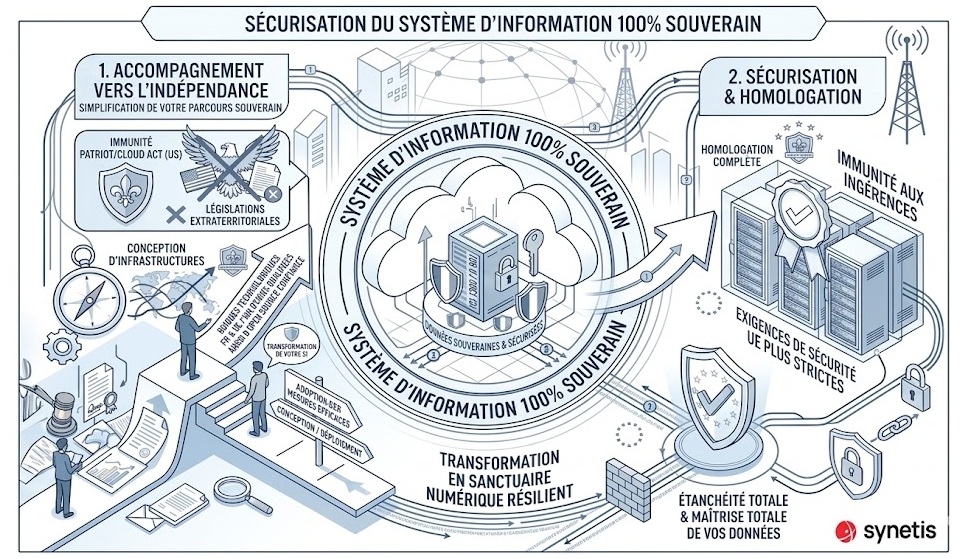
Sovereign information systems
In a context of heightened geopolitical tensions, the protection of your digital assets can no longer depend on solutions subject to extraterritorial legislation. Guarantee your independence with a 100% sovereign Information System.
- Adoption of effective measures against the risks associated with the Patriot Act or the American Cloud Act thanks to a sovereign IS ;
- Design and deployment of infrastructures based on French and European technological bricks, giving priority to ANSSI-qualified solutions or those fromtrusted Open Source;
- Total control over your data and immunity from foreign interference;
- Transform your infrastructure into a resilient digital sanctuary, aligned with the European Union's most stringent security requirements.
Digital sovereignty: take back control
Data independence and security
No longer leave your precious data at the mercy of foreign powers
Transparency and technological confidence
Rely on auditable opensource tools and software, or at least those distributed by French or European players.
Financial optimization and sustainability
Control your costs with open-source software
Do you have an Operational Safety project?
Active Directory audit
Microsoft environments
PKI and certificates
Server protection
Workstation protection
Sensitive information systems
Both a legal obligation and a pillar of your defense posture, compliance with IGI 1300 and II 901 is the essential foundation for protecting your most sensitive data. Implementing these measures can quickly become a complex challenge for your organizations.
Sovereign information systems
Against a backdrop of geopolitical tensions, the protection of your digital assets can no longer depend on solutions subject to extraterritorial legislation. Guarantee your independence with a 100% sovereign Information System.