Hardware penetration testing
Identify security flaws in the components of your devices.
Eliminate technological grey areas
A distinction should be made between two types of hardware pentest:
- Pentesting a workstation (laptop, workstation, etc.);
- Pentesting a connected object (IoT), i.e. a piece of equipment with a specific function (e.g. a measurement or telemetry box).
Pentesting a workstation :
The aim is not to test the robustness of the equipment, but to identify intrinsic weaknesses linked to its design.
In this case, the customer is not the manufacturer of the audited workstation, and therefore has no precise knowledge of its hardware design.
Workstation pentesting enables risk analysis to be adapted to take account of new potential threats linked to the hardware in use.
Pentest IoT :
In the case of IoT pentesting, the customer may be the designer of the equipment to be audited, or he may wish to have an analysis carried out on one or more off-the-shelf devices.
The purpose of the audit is to assess the robustness of the product in the face of known attacks, with the aim of strengthening its security and improving its design if the customer is the designer.
If the customer has purchased an off-the-shelf product, the purpose of the audit is to highlight the risks associated with using the equipment , or to offer a safety trade-off if the customer wishes to choose between several pieces of equipment.
Discover the benefits of hardware intrusion testing
Pentesting a workstation :
- Identification of intrinsic design vulnerabilities: pentesting reveals hardware or architectural weaknesses specific to the equipment, often invisible in a conventional software audit.
- Improved risk analysis: as the vulnerabilities identified are rarely correctable (because they are linked to the design of the hardware), the audit helps to refine the risk analysis, in particular by specifying the conditions or usage profiles to be avoided (e.g. discouraging the use of certain workstations for sensitive users (VIPs, administrators, etc.)).
- Decision support prior to purchase: as part of a comparative study of several workstations (e.g. prior to the renewal of your IT infrastructure), this type of audit enables you to assess the robustness of the equipment available on the market, and guide your choice towards the most secure models.
Pentest IoT:
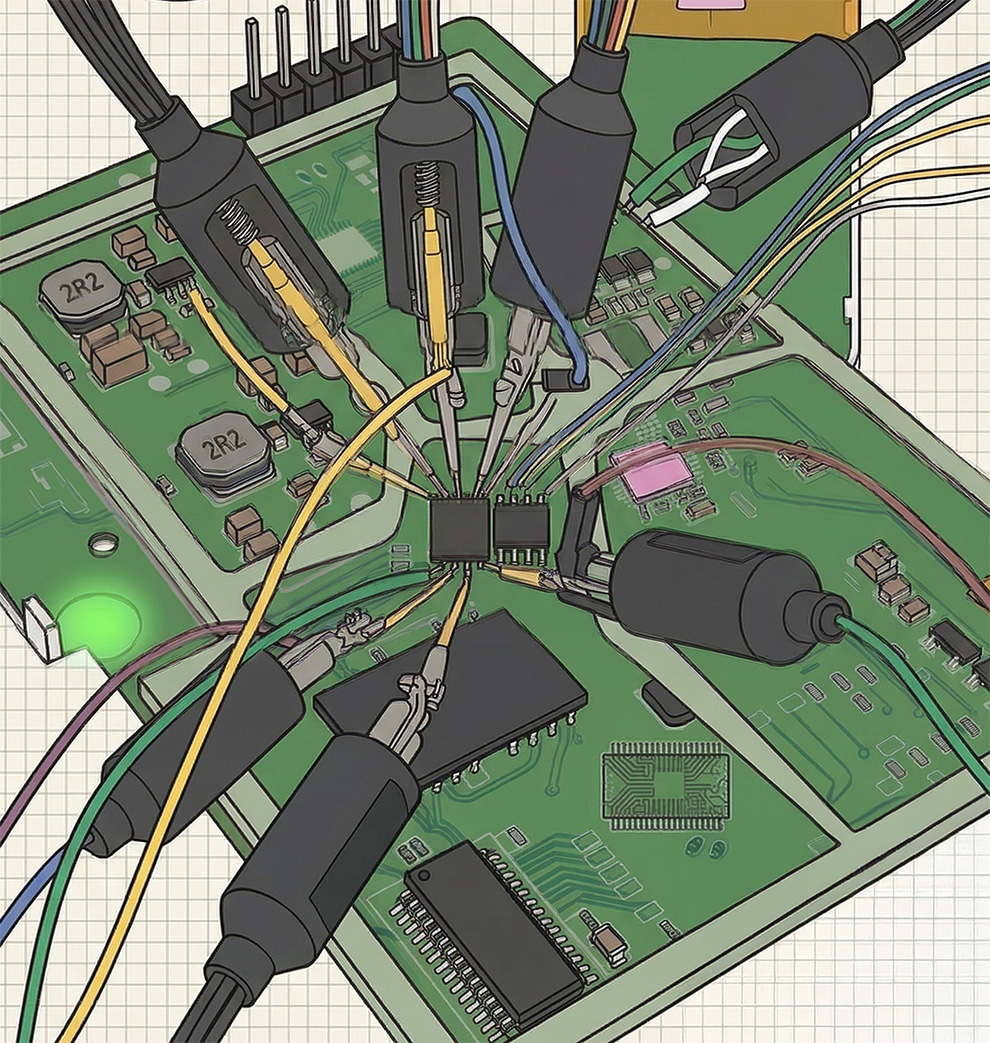
- Assessment of product robustness to known attacks: the audit identifies weaknesses that an attacker could exploit, whether in hardware, software or the interface between the two. This makes it possible to anticipate potential attack vectors before the product is put on the market.
- Improving security right from the design phase: by providing precise technical feedback, IoT pentest enables designers to correct identified vulnerabilities (poor debug access management, lack of firmware signature verification, insecure storage, etc.) and integrate good security-by-design practices.
- Protection of intellectual property and sensitive data: pentesting helps prevent malicious actors from extracting firmware, hijacking equipment functionality, or accessing sensitive information embedded in the product.
- Product enhancement for customers and partners: a product tested and reinforced by a pentest can be presented as more reliable and secure, which is a competitive advantage in a market where cybersecurity is an increasingly decisive criterion.
Rely on a rigorous, proven approach
Pentesting a workstation :
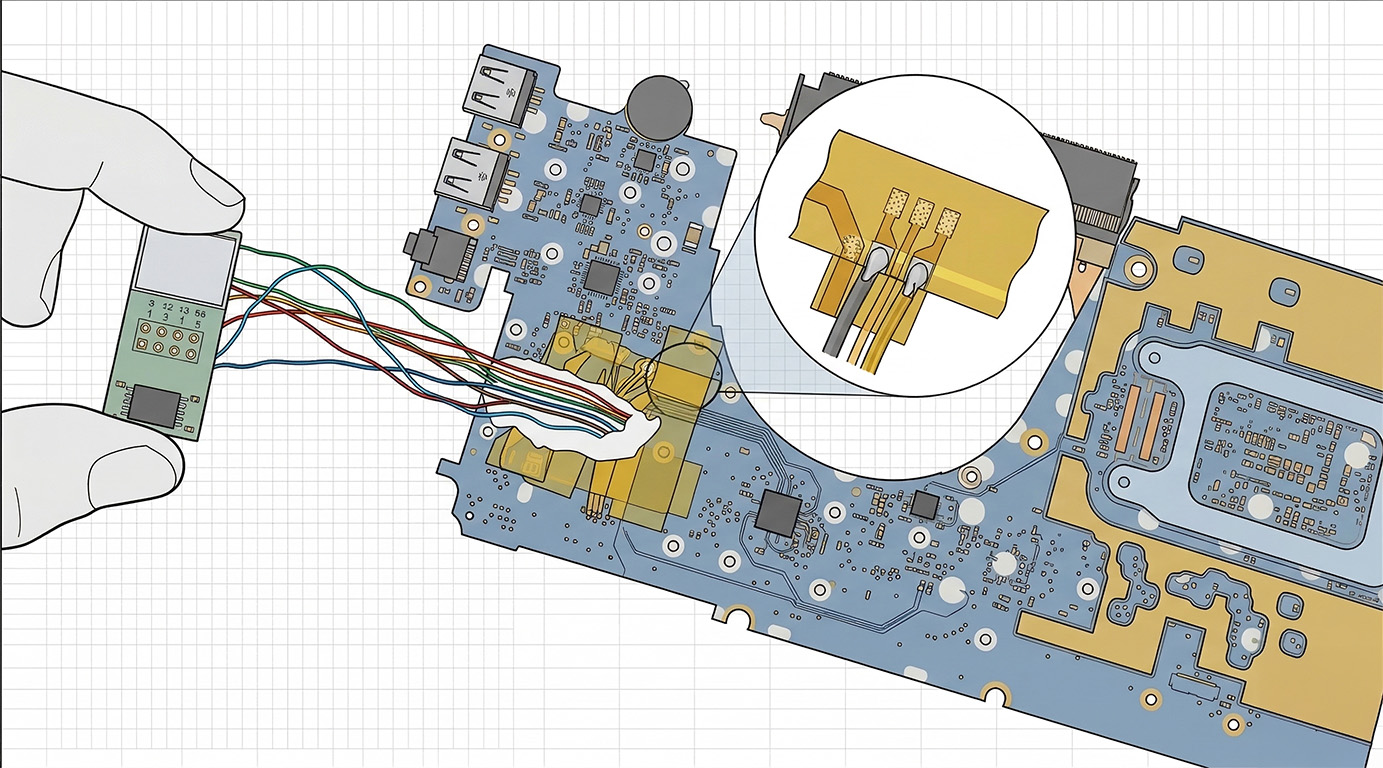
Workstation pentesting is always carried out in black box mode, as the customer has no technical information on the design of the hardware being audited. This is the scenario of a lost or stolen workstation.
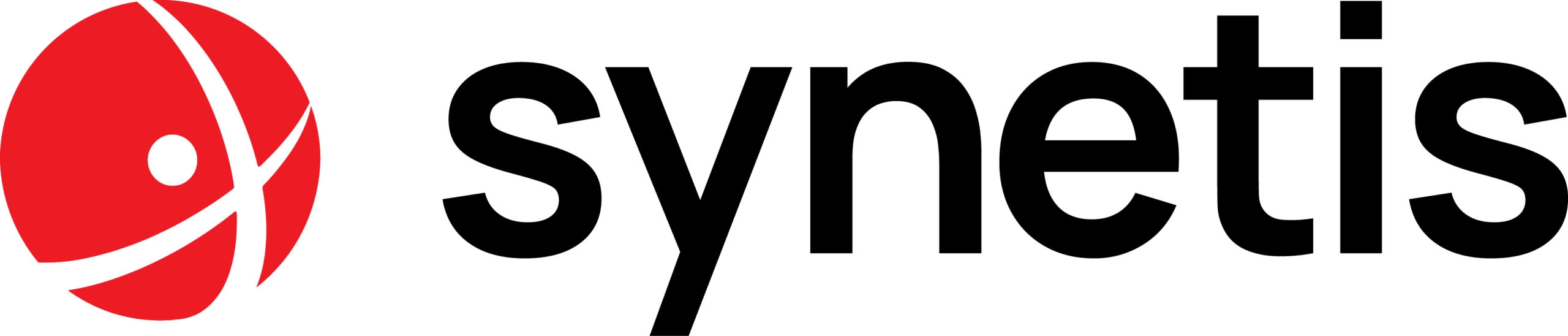
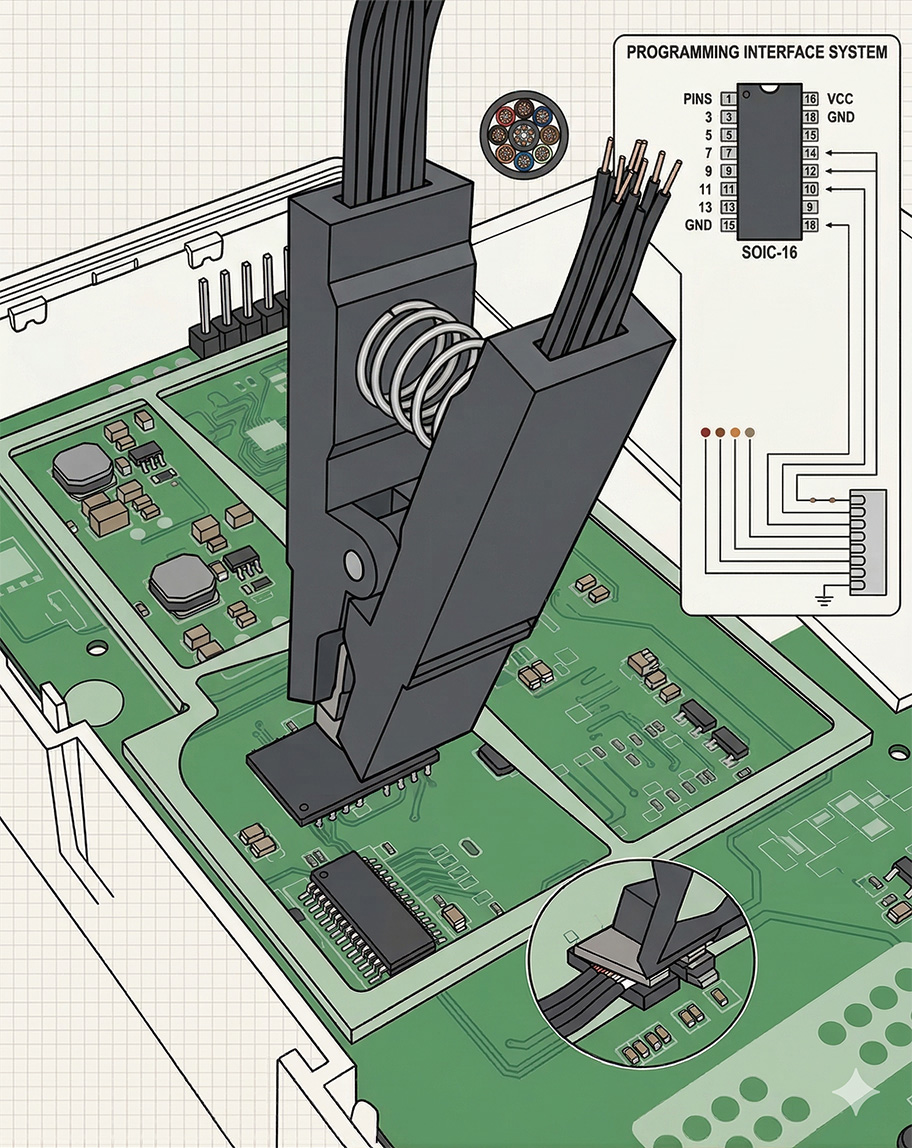
To meet this requirement, a specific methodology was developed, as illustrated in the following diagram.
One of the main challenges of this type of audit is the risk of data destruction or loss.
Being in a black box, the auditors have no useful information on the equipment used or the location of the various components. The documentary research phase will help to remedy this.
However, the methodology also takes into account cases where no information is available, thus minimizing the risk of destruction, while ensuring a good level of analysis.
Pentest IoT:
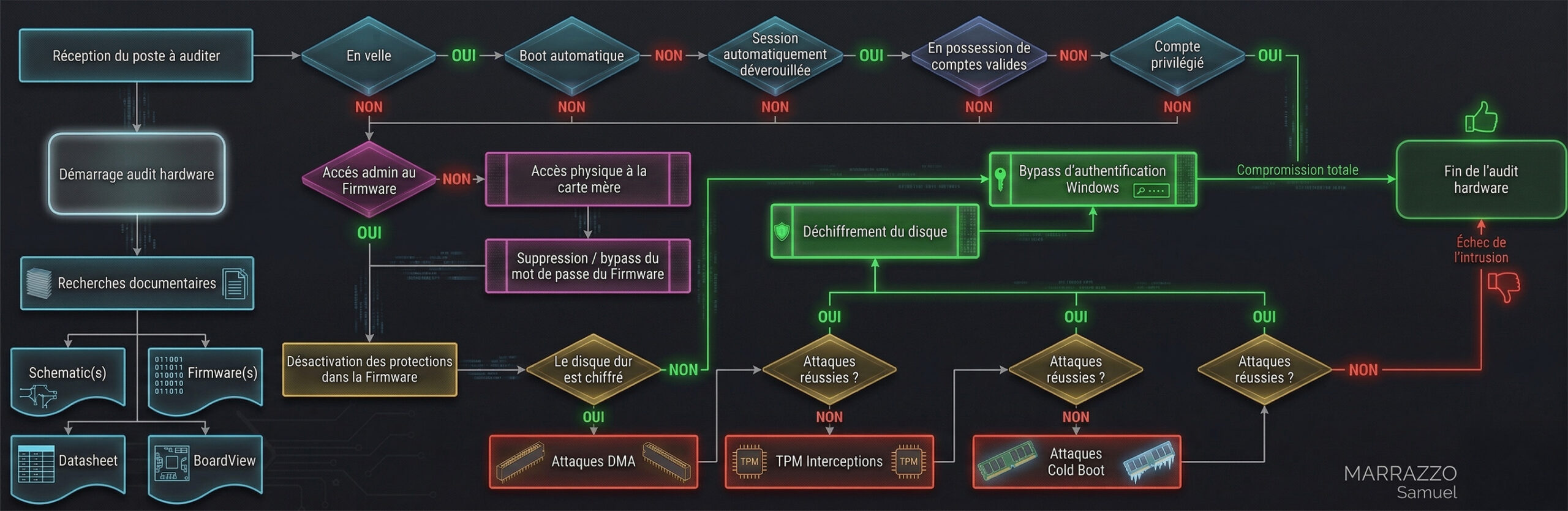
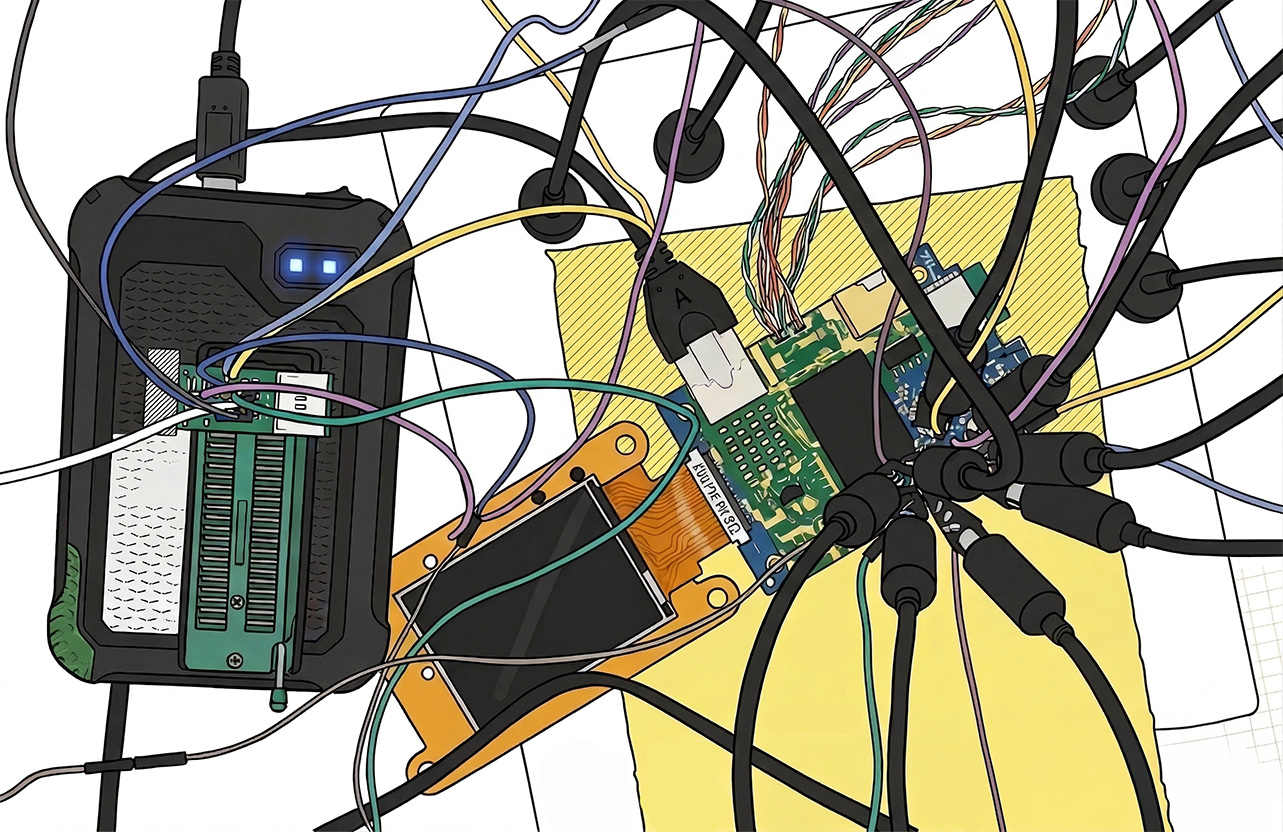
The audit can therefore be carried out in black, gray or white boxes, depending on the information shared.
However, the audit begins systematically in black box mode, in order to simulate the real conditions of an attack carried out without any prior knowledge of the hardware.
The methodology used differs slightly from that applied to substation pentesting. The diagram below illustrates the specific steps involved in an IoT audit.
Unlike substation pentesting, where only two outcomes are possible (total compromise or failure), IoT pentesting can result in a partial level of compromise.
For example, reading and analyzing the firmware may reveal sensitive information, without actually modifying the system’s behavior.
A total compromise is considered to have occurred when modified firmware can be injected and executed on the equipment, thus enabling it to bypass its main function.
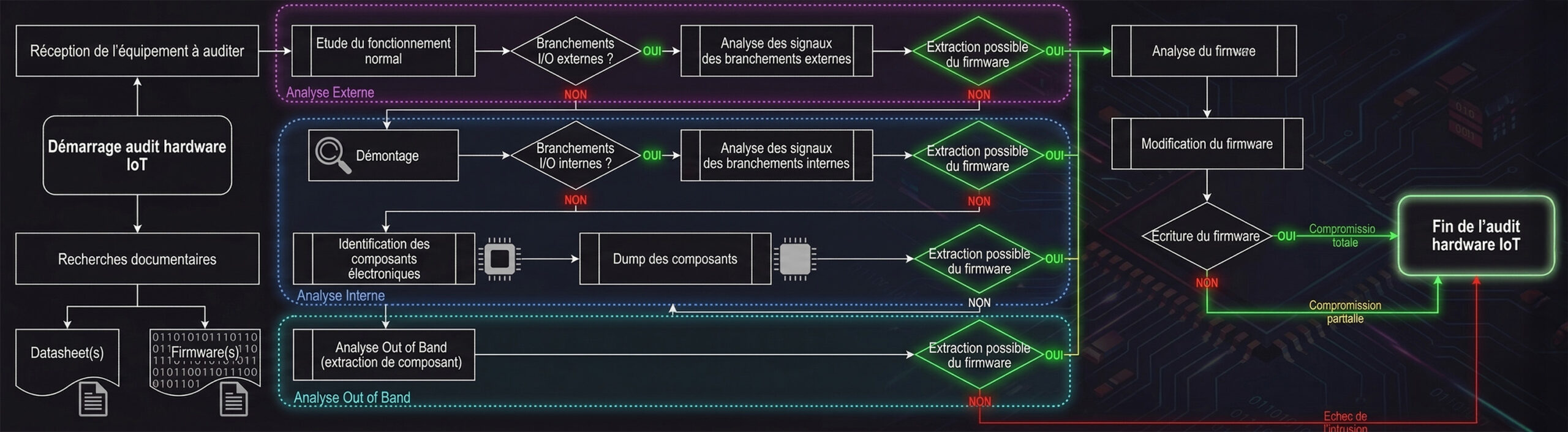
Hardware pentest feedback
If you’d like to find out more about how to carry out this type of intrusion test, you can read the article on a successful hardware intrusion test by Samuel Marrazzo and Louis Distel by clicking here.