Redteam / Purpleteam
A Redteam mission to simulate the behavior of an attacker in real-life conditions against your Information System, as well as a Purpleteam mission to train your BlueTeam team!
Go beyond the intrusion test: simulate the offensive of a determined attacker
Contrary to what you might think at first glance, the Redteam mission is not a penetration test. The Redteam mission is a type of attack designed to simulate the point of view of an external, motivated attacker, whose aim is to break into your organization’s network with a view to carrying out sabotage operations, stealing strategic data,installing ransomware or even persistence software, etc. The Redteam mission is not an intrusion test.
Unlike penetration testing, which is limited to a restricted perimeter (a URL, a Web application, an office computer network, etc.), Redteam’s mission is to target the organization in its entirety: both its online aspects (external exposure, collaborators on Linkedin-type platforms, searching for leaked passwords on the Darknet, etc.) and its physical aspects (intrusion into premises, depositing malicious USB keys, lock-picking, tail-gating).
During a penetration test, the auditors conduct the most exhaustive research possible into the vulnerabilities that could impact the perimeter under test. A Redteam mission, on the other hand, is aimed more at obtaining various trophies, representing key objectives to be achieved by a simulated attacker (exfiltration of sensitive data, access to business software, etc.).
Discover the benefits of a Redteam mission
The Redteam mission provides answers to the following questions:
- What sensitive data can your organization obtain from the Internet?
- Are your employees sufficiently aware of social engineering practices (phishing, spear-phishing)?
- What are the consequences of losing or stealing a company laptop?
- Is someone from outside the organization capable of infiltrating the premises in search of sensitive documents? Are employees aware of these intrusion attempts?
- What compromises are possible from within your company (malicious employees, phishing, etc.)?
- Are your security teams/tools capable of providing “real-time” detection and efficient response during an attack?
Prerequisites for a Redteam mission
We recommend intrusion tests on your infrastructure applications and then on your internal network, to ensure a minimum level of security for your organization.
Once these services have been completed and your overall security level has been strengthened, starting a Redteam mission will enable you to put your cyber posture (solutions, organization, processes) and your security teams to the test.
Rely on a rigorous, proven approach
The role of the sponsor
Redteam’s mission sponsor is the organization’s single point of contact during the service, and its role is to define :
- Boundaries of the perimeter ;
- Sensitive targets ;
- Priority employees or those to be avoided during the phishing phase ;
- Premises targeted by physical intrusion attempts ;
- Authorized methods.
Its aim is to determine the angles of attack that will highlight the sensitive points in the organization’s cybersecurity posture, by validating or proposing trophies.
In the event of a blockage during the service (e.g. due to the detection of security teams), he will be responsible for determining the next stage of the service:
- Assumed breach” approach: this concerns the situation where the auditors encounter a blocking point when attempting to gain initial access to the Information System. The client may then propose the “voluntary” execution of a malicious attack, or VPN access to a first environment, in order to allow the mission to progress;
- Switch to Purple Team;
- End of performance and debriefing of trophies won.
The striker's role
The approach is different from the “classic” one: the auditor takes on the role of an attacker from outside the organization and, unlike a classic approach where he will attempt as many tests as possible in order to test the audited perimeter to the maximum, he will rely on stealth in order to achieve the defined trophies without raising alarms or suspicions from the security teams.
The attacker can then simulate an existing group of real attackers (LockBit, RansomHub, Scattered Spider…) using the same techniques, in order to assess the response of security tools/teams. This simulation can be carried out using the MITRE ATT&CK matrix, which references the techniques, tactics and procedures used by these attackers.
The RedTeam approach aims to simulate realistic (non-destructive) attacks, to thoroughly test the security of a given perimeter. This approach makes for greater efficiency and enables advanced attack scenarios to be carried out, combining logical intrusion with social engineering, phishing and more.
Trophies
Red Teaming is based on predefined trophies agreed between the auditors and the customer.
These can be of various kinds:
- Access to the back-office of an e-commerce site ;
- Access to a customer database ;
- CRM base infiltration ;
- Obtaining Domain Admin access ;
- AD compromise;
- Access to VIP messaging ;
- ERP access ;
- Access to a server room ;
- …
These contextualized trophiesillustrate real risks that could impact your organization. Winning these trophies validates feasibility, exposure and impact.
As a result, a Redteam approach is not destined to be the most exhaustive in terms of security tests against assets (unlike a “classic pentest”), but is geared towards a global, tactical and efficient compromise to get as close as possible to real attacks via trophies.
One of the objectives is also to define the impact of a real attack on an organization, and the cost of the associated measures.
The different routes of intrusion
As part of their Redteam missions, auditors may be required to use a variety of methods, including computer-based (logical intrusion), cognitive (social engineering) and physical (physical intrusion).
Mainly remote, this approach aims to identify the external perimeter of the Information System and exploit potential vulnerabilities to gain access to the organization’s internal network. There are several distinct phases:
- Open-source intelligence phase, which focuses on gathering and analyzing information about the target organization in order to deduce a scope that will be validated and/or refined as the mission progresses: physical sites, employees, partners, service providers, information leaks (internal reports, passwords, etc.), Information System (public addressing plan) ;
- Discovery phase of the external surface of the Information System, aimed at mapping the infrastructures accessible from the Internet: services exposed, technologies used, security equipment..;
- Based on the information obtained above, attempts will be made to compromise the organization’s external surface (exploitation of a vulnerable Web application, reuse of VPN identifiers, etc.). This initial access may enable lateral/pivot movement to other environments;
- If an environment is actually compromised, it makes sense toestablish persistence within it, in order to retain the access gained;
- During the post-exploitation phase, sensitive/business data may be exfiltrated by auditors, particularly if they are the subject of a trophy.
This approach aims to exploit the human factor, often considered the weakest link in the Information System. To achieve this, two main methods can be used: phishing (e-mail attacks) and vishing (telephone call attacks):
- Profiling phase, to identify a list of people to target for the phishing campaign and gather as much information as possible to develop relevant scenarios;
- Definition of phishing campaign scenarios (e.g., sending an e-mail inviting the victim to visit a URL to enter his or her credentials, or to download a malicious file containing a backdoor);
- Campaign execution, typically :
- Phishing : send e-mails, collect indicators (statistics on reception/reading of e-mail/opening of malicious link) and obtain access (backdoor or login).
- Vishing: making a call to execute a malicious attack, or to obtain credentials. The voice factor is used here to be more persuasive in some cases.
A physical intrusion test aims to gain access to the organization’s internal network by attempting to gain access to the organization’s premises (head office, subsidiary or industrial site, for example):
- Reconnaissance phase : perimeter discovery of premises/employees and positioning of access controls, photography of premises, identification of surrounding wireless networks and offensive tests against them, deposit of malicious USB keys, etc. ;
- Physical intrusion: bypassing access controls, manipulating employees, stealing/copying badges;
- Depositing an implant on the internal network to obtain remote access (Wifi or 4G antenna), or using a “rubber ducky” key to rapidly execute a malicious load on a workstation;
- Offensive tests on the internal network.
At the end of this exercise, which can last several weeks, the auditors will draw up a list of vulnerabilities, together with an action plan.
We are committed to restoring the Information System to the state it was in before the start of the financial year.
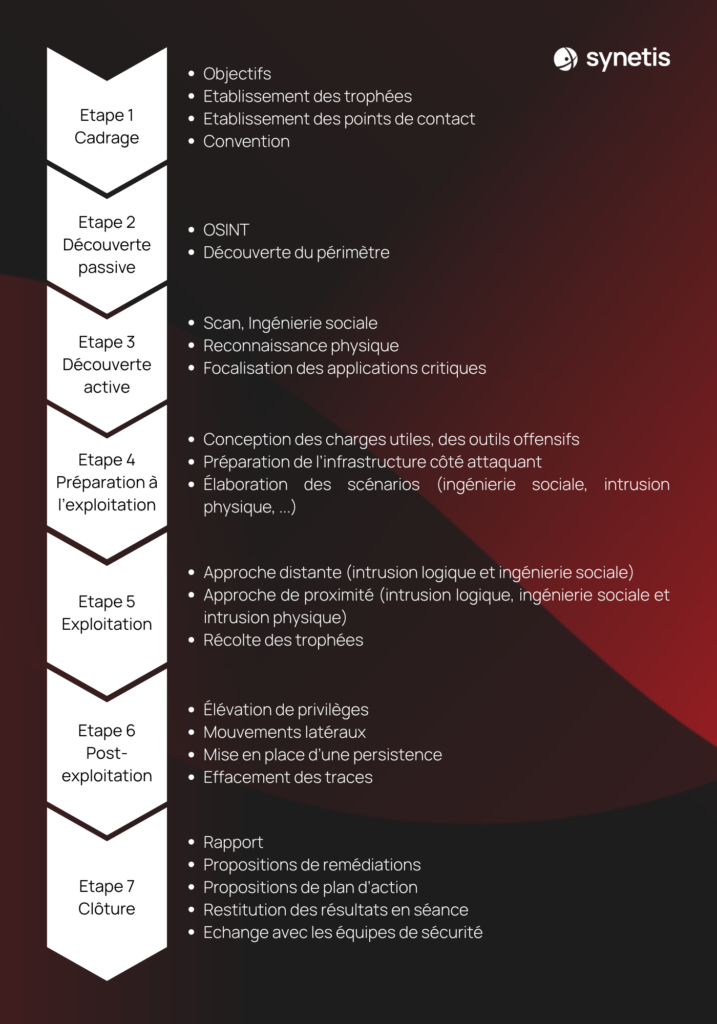
Our Redteam methodology is described below (where phase 2 is carried out continuously throughout the service):
What are the differences between BlueTeam and redTeam?
Unlike the RedTeam, the Blue Team is responsible for defending the organization’s systems and networks. Its role is to constantly monitor the IT environment, detect suspicious activity, respond to security incidents and implement preventive security measures. This function generally falls under the responsibility of a SOC (Security Operations Center) team.
The importance of collaboration between RedTeam and BlueTeam
Although the Red Team and the Blue Team have distinct roles, their collaboration helps to improve the overall level of security of your Information System. The results of Red Teaming exercises provide the Blue Team with valuable information on security weaknesses and areas for improvement. In return, the Blue Team can provide the Red Team with information on the defensive systems in place, enabling the offensive team to improve the realism of its attack scenarios.
PurpleTeam
- Red Team / Blue Team collaboration: The Purple Team is an approach designed to maximize safety efficiency by fostering close, ongoing collaboration between the Red Team (offensive) and the Blue Team (defensive).
- Knowledge sharing: This encourages the sharing of information, techniques and strategies between the two teams. The Red Team communicates its attack methods to the Blue Team, while the Blue Team shares its knowledge of the defenses in place.
- Continuous improvement of Information System defenses, focusing on gaps in the system and exploiting recognized threat classification solutions (MITRE ATT&CK / MITRE D3FEND).
In conclusion, the Red Team mission is a crucial exercise for any organization wishing to put its information system to the test. By simulating realistic attacks, the Red Team highlights vulnerabilities and assesses the effectiveness of existing defenses. If you’d like to take action for your organization, contact the Synetis experts!